Phishing Attack Examples and How to Prevent them
Home / Email Security, Email Protection and Email Filtering / Phishing Attack Examples and How to Prevent themPhishing is arguably the most successful cyber-attack method on the planet. Cybercriminals love to phish people because phishing works. Phishing is a type of social engineering that manipulates employees and individuals into performing actions that benefit a cybercriminal. There have been many research studies into the success rate of phishing; the statistics vary, but they all agree that it is the most utilized method to begin a cyber-attack against an organization. The latest research from Symantec shows that 96% of data breaches start with a phishing email; 1 in 4,200 emails during 2020 was phishing email. Further research from Verizon's 2021 Data Breach Investigation Report shows an upwards trend in phishing-related cyberattacks.
Phishing is successful and damaging, the results of which can be ransomware, a Business Email Compromise (BEC) scam, data breach, identity theft, and so on. Therefore, it is vital to understand the different types of phishing and the types of cyber-attacks associated. Both organizations and managed service providers (MSPs) can use this know-how to understand better how to prevent phishing attacks.
This is the most common form of phishing and one that most of us have come across. This type of phishing uses a spray gun approach to phishing. Cybercriminals indiscriminately send out phishing emails to any email address at their disposal. Scammers can quickly obtain thousands of email addresses by harvesting or from email addresses stolen in data breach incidents. Phishing emails contain links to a malicious website or an infected attachment.
Phishing emails are regular occurrences in both private and corporate email inboxes. These phishing emails often impersonate known commercial brands such as PayPal, Apple, and Facebook. These emails will use an individual's trust in that brand to manipulate their behavior. Phishing emails use tactics such as fear of hacking, urgency, or fear of missing out (FOMO) to encourage an email recipient to click on a malicious link or download an infected attachment.
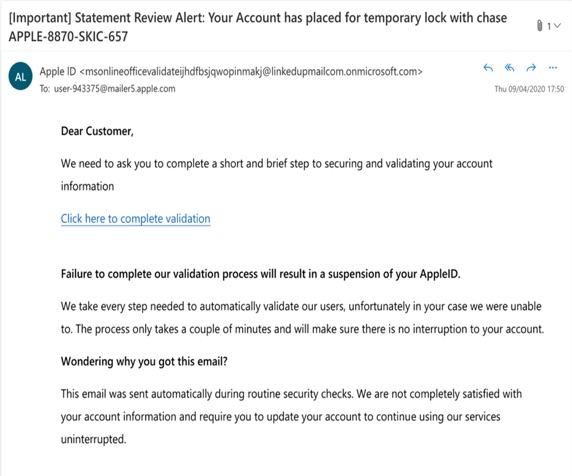
Example of an AppleID phishing email
Email phishing can lead to malware infection via an infected attachment in the email. If the recipient clicks on the attachment, the malware will look for vulnerabilities in software on the user's device and exploit these flaws to install the malicious software. Emails must be scanned and threats detected.
Email phishing can lead to stolen login credentials via an associated spoof website, a user taken to this site if they click on a link in the email or an attachment.
Phishing emails are increasingly challenging to detect as they are designed to evade end user detection. For example, infected attachments such as Word and Excel documents are now less common, and instead, fake image files (.jpeg and .png) are increasingly used to bring malware into people's inboxes.
Spear-phishing is a targeted form of email phishing. An Avanti report found some worrying results when investigating changes in phishing volumes. The researchers found that 85% of respondents spoke of "increasing sophistication" in phishing campaigns. Email phishing works, but spear-phishing takes phishing to new levels of success. Phishers take advantage of a lack of IT skills in an organization to exploit a stressed and tired workforce. Suppose a scammer can get the castle's keys (login credentials to corporate networks/apps); they can make a lot of money and cause damage. Spear-phishing targets those in an organization who have access to sensitive corporate resources, such as system administrators, C-level executives, and those working in accounts payable. Phishing emails work in the same way as email phishing, using psychological tactics to manipulate the behavior of their target.
A scammer will typically carry out reconnaissance research into a company. This will help them locate a likely target, such as a system administrator, who will have the privilege level to giving the scammer access to sensitive resources. For example, the scammer will compose a realistic-looking email that may spoof a corporate app like a Microsoft Office 365 request to download a vital company document. Suppose the target employee clicks on the malicious link and enters their login credentials or other revealing data into an associated spoof website. In that case, the scammer will use this to carry out the next stage in the attack, e.g., infect the network with ransomware.
When spear-phishing scammers go after C-level executives, the phishing attack is known as 'whaling,' aka, catching the big one, a 'whale'. In whaling attacks, scammers will carry out deep reconnaissance of a company, building up the profile of a C-Level executive, such as a CEO or CFO. The resultant spear-phishing email will use extreme tactics and behavioral motivators, such as fear, to manipulate the executive's behavior. For example, the phishing email may contain a threat that the company will be sued to encourage the executive to click on a link or open an infected attachment.
Business Email Compromise (BEC) often has an element of whaling involved. Large and small firms are both at risk of whaling, as this NPR interview with a small business owner discussed: "Mark," an owner of a real-estate firm, told the show how he became a victim of a targeted account takeover attack. Whaling attacks typically try to trick an executive into transferring money or by encouraging a C-level executive to pass approval for the transfer of funds to an accounts payable employee.
Clone phishing is a clever variation of Spear phishing that uses even more sophisticated social engineering tactics. Clone phishing is so-called because the primary technique used by fraudsters is to clone a legitimate email and use that to trick victims. The cloned phishing emails used in this phishing variation are usually based on mass-distributed business emails; for example, an invitation to an online webinar or an urgent request to verify your account with a 'well-known' brand. To generate a cloned email, the hacker first intercepts the target business email; emails are intercepted using several techniques, including unencrypted email channels, which can lead to Man in the Middle attacks (MitM). Once the hacker has a copy of the email, they create a cloned copy with the exact wording, branding, and content as the legitimate email. However, the hackers will insert a malicious link or an infected attachment during email cloning. Once completed, the cloned email is then sent out to the target company employees and contacts.
In the run-up to a Clone phishing attack, the attackers will have conducted intelligence on the target company. During the construction of the cloned email, the attackers will add malicious elements, such as an infected attachment or a link to a spoof website. The hackers will ensure that the spoof website matches the target brand. If a Clone email recipient clicks the malicious link in the cloned email, they will end up on the spoof website, which is engineered to steal login credentials and other data. If login credentials are stolen, they will be used to gain unauthorized access to corporate devices and the network. Once the hackers have access to the corporate apps and network, they will use that access to further attacks on the organization. These attacks include infecting the network with ransomware, stealing data, and committing fraud such as Business Email Compromise (BEC) and other financially motivated cyber-crimes. Even if the login credentials stolen are not privileged credentials, hackers will use techniques such as lateral movement to escalate login privileges. Recent research shows that phishing is becoming the most common method to deliver ransomware, with Q3 2022 showing a surge in the use of phishing for ransomware infections.
Vishing is a form of phishing that uses a mobile phone to extract information from an individual or direct them to carry out a behavior that results in stolen data. Often vishing is used in combination with other phishing types, such as spear-phishing. Whaling, for example, may involve an initial phone call from a scammer to extract information that then leads to a whaling email. Vishing covers a spectrum of sophistication, from spray gun-type vishing messages that target the public to focused spear-vishing. The latter may work as part of a scam that steals large sums of money from a business. An excellent example of this was a 2018 scam that involved a phone call that used a fake voice to trick a CEO into transferring $240,000 to a fraudster.
A recent FBI notice explains how scams may use multiple steps during a cyber-attack, some of these steps focusing on privileged users. These attacks often involve reconnaissance using vishing that then utilizes spoof web pages that are used to steal second-factor authentication codes, thereby bypassing traditional forms of protection.
PhishTitan is an advanced phishing protection solution for companies using M365, powered by AI technology. Sign up for our Free Demo to learn more.
Free DemoSmishing is a form of phishing that uses mobile messaging channels, such as SMS text and WhatsApp, etc., to send out a phishing message. Like its email counterpart, the smishing message uses psychological tricks to manipulate targets.
Like all social engineering attacks, smishing uses tricks to manipulate users into doing as the scammer wants. The fraudster uses tricks such as instilling fear into the recipient of a phishing message: financial smishing is a form of smishing where the message will look like it is from a well-known bank. The message will be composed to scare the recipient into thinking their bank account is compromised. The smishing message typically contains a URL that will take the person to a fake bank website where their actual bank login credentials will be stolen, and their bank account hacked.
Barrel phishing or "Double-Barrel" phishing is successful because it uses emails to build trusted relationships with the victim. Barrel phishing uses a double-whammy email system of 'bait and sting': the first or 'bait' email is sent to the target to help make the victim feel that a legitimate person is emailing. This bait email is then followed by the second part of the Barrel phishing attack, i.e., the 'sting' or malicious email. Trust is the core element of a Barrel phishing attack; the attacker uses the bait email to build a trusted relationship with the email recipient. This trust is then exploited in the follow-up email containing malicious elements. Barrel phishing attacks are designed to steal login credentials and other data that is used in other cyber-attacks, including Business Email Compromise (BEC) and ransomware infections.
Barrel phishing attacks work by building a trusted relationship to ensure a successful attack. Any targeted phishing attack will require the cybercriminal to conduct intelligence-gathering exercises to find out as much as possible about the target. Once the attacker has the information needed, they will create a believable first email that is non-malicious. This first email typically reflects a brand or company known to the victim to help build rapport. The first Barrel email is designed to engage the recipient and make them feel comfortable and trust the sender. Soon after delivering this first non-malicious email, the second Barrel email will be sent to the same recipient. This second email does contain malicious content. Because the first email was a relationship-building exercise, the recipient is more likely to engage with any links or attachments in this second email. They will be sent to a spoof website designed to steal login credentials or other sensitive data if they click a link. Alternatively, the second Barrel email may contain an attachment; if the victim opens this attachment, it may end in ransomware or other malware infection. Barrel phishing is a first part of a chain of attack that can end in financial scams, such as Business Email Compromise or ransomware attacks; the Ponemon Institute found that 54% of security incidents were caused by credential theft.
Many phishing campaigns are dependent on fake websites to carry out an attack, so it is essential to note the part that spoof websites play in email phishing attacks. Fake or spoof websites are typically sophisticated and realistic, using similar domain names to the brand they spoof. In addition, the sites usually use digital certificates to make the website look 'secure' - the certificates setting the site URL as beginning with an HTTPS (S for secure). The Anti-Phishing Working Group (APWG) identified 316,747 such websites in December 2021.
The spoof website is often a companion to a phishing campaign. A malicious link in a phishing, spear-phishing, or smishing message, will take a recipient to the companion spoof website. The fake webpage usually reflects the brand that the phishing message spoofs, for example, a Microsoft Office 365 login page. Once the target has navigated to the spoof website, they are requested to enter their login credentials (or other personal details). Once submitted, the data is sent to the hacker behind the scam, who then uses them to log in to the actual site.
PhishTitan is an advanced phishing protection solution for companies using M365, powered by AI technology. Sign up for our Free Demo to learn more.
Free DemoProtection against phishing requires a layered approach to anti-phishing protection; by using multiple layers of protection, an organization is more likely to stop the threat before it becomes an incident:
This is a fundamental step in phishing prevention. Security awareness training, augmented with simulated phishing exercises, will make employees aware of the various phishing attack methods.
Prevent phishing emails from landing in an employee's inbox using a multi-layered spam filter. The filter must be configurable to allow legitimate emails to keep phishing emails out.
Any navigation to a fake website, such as via a mobile device, can be prevented by deploying a content filter. For example, an HTTPS content filter checks a website to ensure it is not a phishing site before allowing a user to enter the site; any sites identified as phishing are blocked.
Effective phishing prevention needs to be scalable across multiple types of devices. The email and content filters must be able to be easily configured and updated from a central console. A cloud-based system provides central management and is suited to deployment and management from a managed service provider (MSP)
Take our Security Training Awareness Quiz
PhishTitan is an advanced phishing protection solution for companies using M365, powered by AI technology. Sign up for our Free Demo to learn more.
Free DemoPhishing attacks can occur in any format, over almost any communication medium. Whenever cybercriminals use these communication channels to impersonate trusted contacts and institutions, it’s a phishing attack. Preventing those attacks requires an advanced, multi-layered security tech stack. SpamTitan is an important part of the solution to this problem.
Phishing, spear phishing, and whaling are some of the most common types of phishing attacks. They are distinguished by the amount of research and in-depth knowledge attackers leverage when targeting victims. Highly automated phishing attacks may only use publicly available data, while elaborate whaling attacks rely on private data.
SpamTitan provides increased security against every kind of email threat. However, no security solution can guarantee success against 100% of all known and unknown threats. Organizations that deploy a strong, multi-layered security tech stack have a much better risk profile than ones that don’t.
Whaling attacks may leverage sensitive personal information that isn’t publicly available to deceive targets. SpamTitan can scan for keywords that indicate emails containing sensitive data and reference its behavioral models to determine whether that data is coming from a trusted source or not.
SpamTitan is designed to keep malicious emails out of users’ inboxes. When SpamTitan detects a malicious email, it quarantines the email so that it doesn’t pop up at the top of the recipient’s inbox. A trained security analyst can then investigate the email and determine whether it represents a threat.
SMS network architecture doesn’t support advanced security features. That’s why cybercriminals increasingly rely on SMS to send fraudulent messages targeting victims. However, SpamTitan can still protect users from clicking on malicious links contained in emails, which improves your overall security posture against all phishing threats – including smishing attacks.
Yes, SpamTitan uses advanced machine learning models to identify and block advanced email phishing attacks, including ones that leverage zero-day vulnerabilities. SpamTitan uses a variety of technologies, like URL rewriting and click time verification to achieve best-in-class email security.
The SpamTitan deployment process is simple, and the software requires very little ongoing maintenance. Once deployed, SpamTitan will immediately begin analyzing and filtering email threats to reduce your organization’s risk profile. There is no need for additional input or workflow changes from email users.
SpamTitan provides out-of-the-box functionality for a wide range of phishing attacks, including the most sophisticated types of attacks. SpamTitan users can immediately improve their security posture within minutes of subscribing to the service. The software supports configuration for customized deployments, but is capable of mitigating email risks immediately.
Malicious links can lead to many different kinds of attacks. Safeguarding your data is the best way to respond to phishing incidents. You should start by changing your passwords and enabling multi-factor authentication on apps and services you use. Consider signing up for additional protection, as well.

