
Rise of Phishing-as-a-Service (PhaaS)
Selina CoenWhy Strong Phishing Protection Matters More Than Ever with the Rise of Phishing-as-a-Service (PhaaS)
Content filtering is part of a multi-layered approach to protecting against malicious cyber-attacks. Microsoft Office 365 is an incredibly popular platform. Globally, over one million companies using Office 365, 600,000 of them in the U.S. Popularity at this level means that the brand and platform are also popular with cybercriminals, as fraudsters love to spoof well-known and trusted brands. Several reports have identified Microsoft Office 365 as the ‘phishers favorite’.
To protect our use of Office 365 we can turn to technology in the form of a content filter or more specifically DNS Filtering, but what is this, why is it needed, and how can it help?
Office 365 has always been a target for cybercriminals because it is a well-known and trusted brand. This trust can be manipulated by cybercriminals and used to power social engineering-based cyber-attacks. Organizations need to be aware of the areas where these threats are focused so that they can harden systems and processes against them.
Phishing is a common method used by fraudsters to steal login credentials to Office 365 user accounts. Once into an account data and sensitive information can then be stolen. The Covid-19 pandemic saw heightened attacks against the platform with the targeting of Office 365 users with phishing emails. A recent example of a Covid-19-related phishing campaign had the title, “COVID-19 Training for Employees: A Certificate for Health Workplaces.” Email recipients were asked to click on a link that took them to a spoof Office 365 login page. If the user entered their Office 365 credentials, they were stolen and used to login to the real Office 365 portal.
Executive users of Microsoft Office 365 are also at risk. Trend Micro identified a Business Email Compromise (BEC) campaign that uses phishing and spoofs Office 365 login pages in an attempt to steal privileged user login credentials. Once the fraudster is in possession of the Office 365 executive user account, they then create invoices and/or tamper with banking information to redirect money to their own bank account via fund transfer requests. To date, over 1000 companies worldwide have been targeted with this method of attack.
DNS Filtering is part of a multi-layered approach to protecting against malicious cyber-attacks. But to understand what DNS Filtering is, we need to look at how a certain aspect of using a website works.
To allow the internet to be used by humans and machines, the internet uses something known as the Domain Name System or DNS to match human operators with the wider internet and protocols. To navigate to a website and read the contents of that site, the following takes place:
The human: When we go to a website we type in a human understandable ‘URL’, e.g. mycomany.com.
The browser: A web browser communicates using an Internet Protocol (IP) address, that looks something like 30.99.11.89.
The DNS server: A DNS server translates a domain name to an IP address, facilitating the loading of web pages and other internet resources. This means humans don't have to remember numbers, only human readable names.
Cybersecurity protection is not something that can be done in isolation. Cybercriminals use multiple channels, across complex attack-chains to carry out a successful cyber-attack. Cybercriminals use layers of tactics to steal credentials and data. To protect our organization against these multi-layered cyber-attacks we need to put multiple layers of defense in place.
A DNS Filter provides a layer of protection against incoming web-based cyberattacks. It does this by preventing users from going to malicious websites. This is an important layer of an organization's cyber-defense that will kick in if other measures fail.
Let’s assume that a phishing campaign is cleverly put together so that spam filters do not spot the tell-tale signs of a phishing message. There are around 14.5 billion spam mail messages per day and phishers are continuously improving their emails to obfuscate their tactics, so this is possible.
Let’s also assume that the phishing campaign is highly sophisticated, and the email is well-composed to fit with a current hot topic to trick users (like Covid-19 healthcare training). If the phishing email arrives on an unsuspecting (or even trained) employee, they can be easily tricked into clicking a malicious link.
This is where DNS Filters excel.
A DNS Filter provides an extra layer of protection by preventing users from visiting malicious websites contained in links in phishing emails.
The steps to protection are:
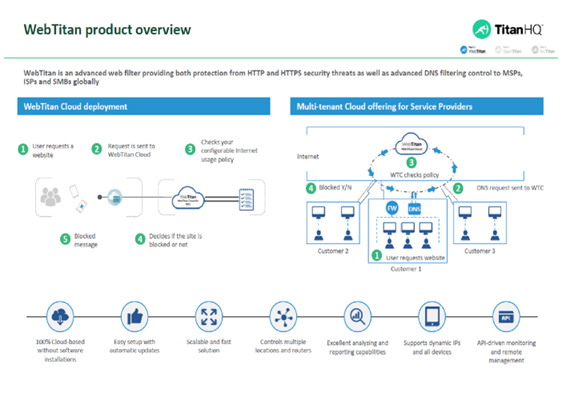
The WebTitan DNS content filter protects against the chances of an employee visiting a malicious website. But the solution also goes beyond protecting against employees navigating to malicious websites. WebTitan allows IT teams to block malware downloads, monitor internet activity, and carefully control the types of websites their remote users can access on corporate devices.
With the sophistication and attention to detail of modern web-based cyber-threats, this multilayer approach to protecting your corporate resources is essential.
- 700 million URL’s crawled daily providing crowd-sourced categorization and threat protection.
- 200 languages covered
- 5 trillion search queries examined monthly
- 3 million malicious URLs and phishing sites blocked at any one time
- 100,000 new malicious and phishing site entries daily
- 300,000 malicious URLs revisited every single day
- 100% coverage of the Top 1 Million most visited websites
- 99% coverage and accuracy of the entire active web, the industry leader.
- 53 Unique Content Categories
- 200,000 queries per second/per instance
- 5 microseconds for database lookups
- 1 Vital DNS Security Layer
Here's how our WebTitan DNS content Filter works:
If you have not yet implemented a DNS content filtering solution and would like more information on how it can protect against cyberattacks on remote workers, contact the TitanHQ team today.

Why Strong Phishing Protection Matters More Than Ever with the Rise of Phishing-as-a-Service (PhaaS)

Deepfakes are becoming increasingly realistic and accessible, posing serious cybersecurity and reputational risks for businesses. Learn how they work, the threats they pose, and what IT teams can do to...

Explore the critical importance of robust email security in 2025. Learn how advanced threats like phishing and business email compromise are evolving, and discover strategies to protect your organization effectively.

Call us on USA +1 813 304 2544 or IRL +353 91 545555
Contact Us