WebTitan Web Filtering Categories - An Overview
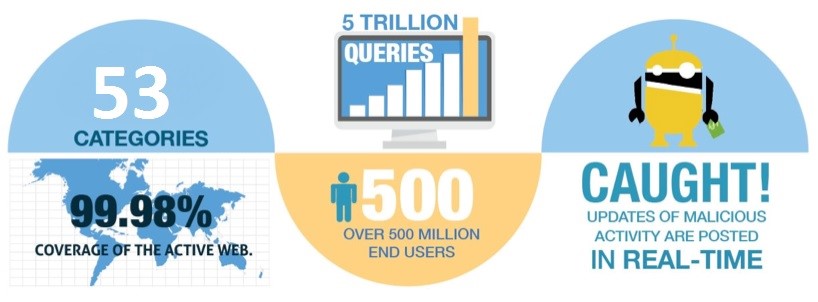
TitanHQ’s high-quality web filter, WebTitan, delivers a highly accurate and comprehensive URL classification database with full ActiveWeb coverage. It supports advanced malicious website detection, zero-hour protection, and continuous updates, with flexible deployment options, either as an appliance or fully hosted in the cloud.
WebTitan’s powerful URL policy engine provides 53 predefined website categories along with eight customizable categories, giving you granular control over which sites users can access. The intuitive cloud-based interface enables fast policy creation and management at the network, group, user, device, or IP level, giving you complete oversight of your organization’s web activity.
Built for scalability, WebTitan supports everything from small-business deployments to large ISPs and multi-million-user environments, while maintaining exceptional URL query performance. Its market-leading accuracy, extensive coverage, and advanced threat detection are also available through an easy-to-integrate API.
Our web filtering categories are powered by real-time analytics and threat intelligence derived from 500 million users and over 5 trillion web queries per month, providing coverage of 99.9% of the active web.
Did You Know?
businesses experienced a DNS attack
malware & spyware domains categorised a day
predefined categories by default
of websites tested by Google for malware were infected
Web Filtering Provides Protection
These categories enable you to protect business users by:
1. Blocking access to categories including malware, phishing, malicious sites, and spam sites.
2. Adhere to corporate usage policy by blocking access to categories such as adult, pornography, gambling, hate speech, and nudity.
3. Create usage policies to ensure resource protection, controlling or limiting access to social media, social sites, video, or streaming sites.
WebTitan uses proprietary AI-based and Machine Learning categorization engines to process millions of URLs daily.
WebTitan Web Filtering Features:
Coverage.
WebTitan’s network of 500 million users ensures over 99.9% coverage of the active web traffic
Accurate.
WebTitan uses a combination of machine learning and human quality assurance to maintain high accuracy, and it is updated in real-time
Fast.
WebTitan makes a decision in about 5 microseconds by using a local SDK, supplemented by cloud updates of uncategorized URL’s
Granular.
53 different web categories in over 200 languages
Easy Integration.
WebTitan is available in an easy-to-integrate API
Flexible Pricing
WebTitan is priced efficiently and on a flexible basis
Real Time Malware Detection
Our market-leading content categorization and malicious URL detection solution, WebTitan, delivers real-time, automated updates as new content and threats emerge. The platform identifies over 60,000 new malware variants every day, ensuring continuous, up-to-the-minute protection.
The 53 Categories available in WebTitan for Web Filtering and URL Filtering:
1. Alcohol:
Web pages that promote, advocate, or sell alcohol, including beer, wine, and hard liquor.
2. Anonymizer:
Web pages that promote proxies and anonymizers for surfing websites with the intent of circumventing filters.
3. Art:
Theater, museums, exhibits, photography, and digital graphic resources.
4. Business/Services:
General business websites.
5. Cars/Transportation:
Vehicles, including selling, promoting, or discussing.
6. Chat/Instant Messaging:
Communication through chat or Instant Messaging services, as well as sites with information about Instant Messaging communication or chat rooms. A particularly popular category is the increased popularity of Facebook Messenger. WebTitan can allow access to Facebook while blocking Facebook Messenger.
7. Community Sites:
Newsgroup sites and posting, including forums and bulletin boards.
8. Compromised:
Web pages that have been compromised by someone other than the site owner and appear legitimate but contain malicious code. A very dangerous category in terms of malware threats.
9. Computers and Technology:
Sites with information about computers, software, hardware, peripherals, and computer services.
10. Criminal Skills/Hacking:
Activities that violate human rights, including murder, sabotage, bomb building, etc. Information about illegal manipulation of electronic devices, encryption, misuse, and fraud. Warez and other unlawful software distribution.
11. Dating:
Web pages that promote relationships, such as dating sites and marriage sites.
12. Download Sites:
Shareware, Freeware, and other software. P2P sites and software.
13. Education:
Educational institutions and schools. Educational and reference materials, including dictionaries, encyclopedias,
14. Entertainment and Videos:
Websites for videos, TV, and motion pictures, including celebrity sites and entertainment news.
15. Finance:
Bank, insurance companies, and other financial institutions. Active trading of certificates and stocks.
16. Gambling:
Web pages which promote gambling, betting, lotteries, casinos and betting agencies involving chance
17. Games:
Web pages consisting of computer games, game producers, and online gaming
18. Government:
Government organizations, departments, or agencies. Includes police, fire, and hospitals.
19. Hate Speech:
Web pages that promote extreme right/left wing groups, sexism, racism, religious hate, and other discrimination
20. Health
Personal health and medical services, including sites with information on equipment and procedures.
21. Home/Leisure:
Sites with information about home improvement and decorating, family, gardening, hobbies, etc.
22. Humor:
Web pages that include comics, jokes, and other humorous content
23. Illegal Drugs:
Web pages that promote the use of information about common illegal drugs and the misuse of prescription drugs and compounds
24. Job Search:
Web pages devoted to job searches or agencies, career planning, and human resources
25. Mature:
Sites not appropriate for children. Includes sites with content about alternative lifestyles, profanity, etc.
26. Military:
Web pages sponsored by the armed forces and government-controlled agencies
27. Miscellaneous:
Content Servers are used to supply supplementary website content, or web pages that do not clearly fall into any other category
28. Music:
Web pages that include internet radio and streaming media, musicians, bands, MP3 and media downloads
29. News:
Web pages with general news information, such as newspapers and magazines
30. Non-profits:
Clubs, communities, unions, and non-profit organizations.
31. Nudity:
Web pages that display full or partial nudity with no sexual references or intent
32. Online Ads:
Web pages strictly devoted to advertising graphics, banners, or pop-up ad content
33. Personal Webpages:
Websites about or hosted by individuals. Communication through blogs and guestbook servers. Information on personal hobbies and activities.
34. Pharmacy:
Web pages that include prescribed medications and information about approved drugs and their medical use
35. Phishing/Fraud:
Manipulated web pages and emails used for fraudulent purposes, also known as phishing
36. Politics and Law:
Sites that promote political parties and interest groups. Information on elections and legislation. Sites that offer legal information and advice.
37. Pornography/Sex:
Explicit sexual content is unsuitable for persons under the age of 18.

WebTitan filters objectionable sites like pornography
38. Portal Sites:
General web pages with customized personal portals, including white/yellow pages
39. Real Estate:
Web pages possessing information about renting, purchasing, selling, or financing real estate, including homes, apartments, office space, etc.
40. Religion:
Religious sites and information. Includes Sects, cults, occultism, and religious fundamentalism.
41. Restaurants:
Food, dining, and catering services, including sites that provide reviews, advertisements, or other promotions.
42. Search Engines:
Web pages supporting the searching of the web, newsgroups, pictures, directories, and other online content
43. Shopping:
Online shops, catalogs, and online ordering. Auction sites and advertising. Classified ads. Excludes shopping for products and services exclusively covered by another category such as health.
44. Social Networking:
Social networking web pages and online communities built around communities of people where users "connect" to other users
45. Spam:
Products and web pages are promoted through spam techniques. Very important for malware protection.
46. Sports and Recreation:
Sports teams, fan clubs, and news. Recreation activities, including zoos, public recreation centers, pools, and amusement parks
47. Spyware and Malicious Sites:
Sites or software that install on a user’s computer with the intent to collect information or make system changes without the user’s consent. A must-block category.
An essential element of any web filter is blocking malicious sites
48. Tobacco:
Web pages promoting the use of tobacco-related products (cigarettes, cigars, pipes)
49. Translator:
Web pages that translate languages from one to another
50. Travel:
Web pages that provide travel and tourism information, online booking or travel services such as airlines, car rentals, and hotels
51. Violence:
Web pages that promote questionable activities such as violence and militancy
52. Weapons:
Web pages that include guns and weapons
53. Web-based Email:
Web pages that enable users to send and/or receive email through a web accessible email account
WebTitan Web Filtering Benchmarks
Accuracy
- 99.9% accuracy
- Proprietary AI-based and Machine Learning categorization engines process millions of URLs daily with Q/A and “supervised learning” being provided by the review of tens of thousands of URLs daily by multi-lingual Q/A teams
- Tracks Accuracy across each Language/Category pair (i.e. English/Dating) on an hourly/daily/weekly basis with automated tuning of AI algorithms based on performance
Coverage
- 99.9% coverage of the ActiveWeb
- Validates coverage against the Alexa global and country-specific lists daily
Malicious Detection
- Identifies new malicious URLs and IPs daily
- Pioneer in Malicious Website detection techniques
Time to Categorize New URLs / IPs
- New URLs are automatically identified and forwarded for contextual categorization and malicious detection processing
- Average time to process/categorize new URL is less than 1 minute
Time to Respond / Correct Miscategorized URLs
- 24x7 support for miscat submission handling
- Average less than 20 minutes to research and correct, if necessary, any miscat submissions
- Any corrections are immediately distributed
Updating / Database Freshness
- Provides real-time updates throughout the day
- Provides a full incremental file update daily
- You have the option of getting real-time updates throughout the day as well as performing full-time updates daily
- You have immediate protection against the newest threats, malicious sites, objectionable/porn sites
Category Granularity / Category Mapping
- 53 categories in our content, objectionable and malicious categories
- Categories can easily be “mapped” to your specific category taxonomies if needed
Language Support
- WebTitan includes categorized URLs from over 200 languages
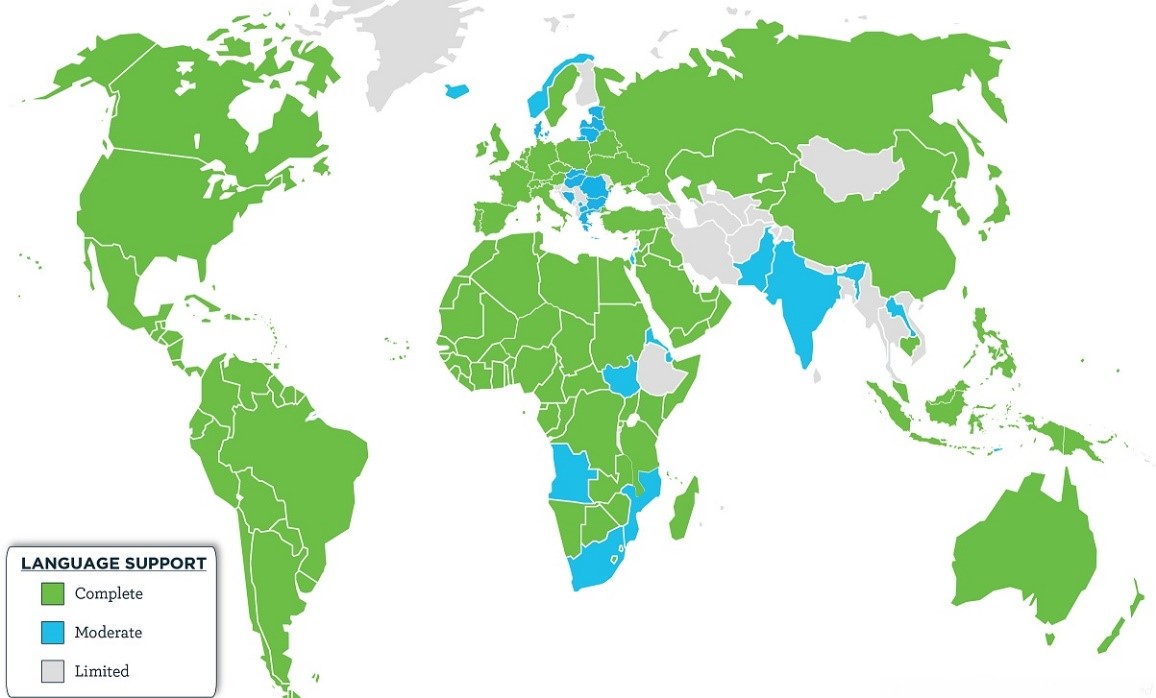
WebTitan URL Filtering supports over 200 languages for 6,500 customers globally

Susan Morrow
- DNS FILTERING
- WEB FILTERING
- CONTENT FILTERING
Talk to our Team today