PhishTitan & SpamTitan Comparison With IRONSCALES
In 2023, cybersecurity experts saw increased phishing attacks with malicious URLs, ransomware, and malware attachments as the top three payload deliveries. Many targeted enterprise businesses use Microsoft M365 and rely on its integrated security. Because attackers know that MS M365 is expected in the enterprise, sophisticated threats are built to bypass Microsoft’s native email security. Bypasses were successful, and businesses fell victim to hacking, ransomware, and phishing.
Because businesses can’t rely solely on MS Office’s integrated email security, they search for a third-party system that complements it.
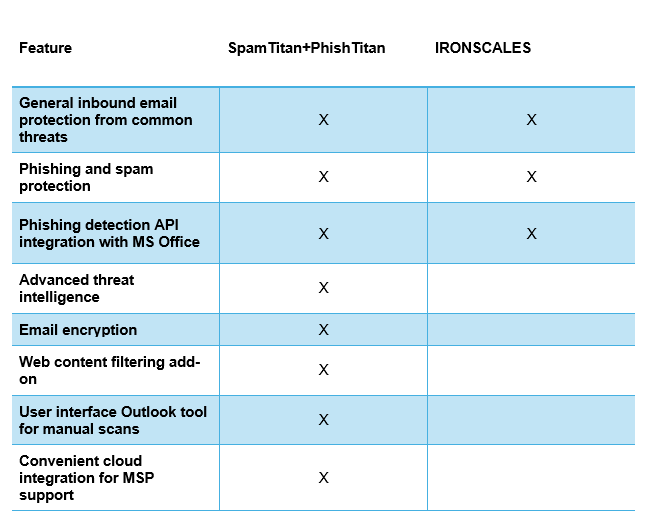
Differences Between PhishTitan+SpamTitan and IRONSCALES
TitanHQs PhishTitan and SpamTitan might look similar to IRONSCALES, but both products have technical differences affecting efficiency, accuracy, integration, and administrator convenience. For example, both IRONSCALES and PhishTitan block phishing attacks, and both IRONSCALES and SpamTitan block nuisance and malicious spam messages. All three solutions work with Microsoft M365 as a complementary cybersecurity and email protection solution to block email-based threats.
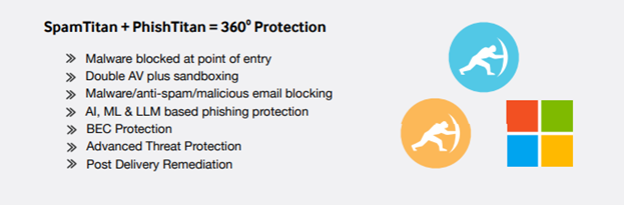
A few benefits that come with the PhishTitan and SpamTitan working together:
- A secure email gateway (SEG) to block threats before they reach your internal infrastructure
- API connectors to integrate anti-phishing filters with your M365 email service
- Artificial intelligence (AI) to detect zero-day threats and sophisticated phishing bypasses
- Integration with Microsoft M365to block phishing threats that bypass native Microsoft security
- Remediation scans of all user inboxes post-delivery and receipt of threats
- Machine learning and LLM-based detection for sophisticated phishing scams
- Dashboards and reports to review quarantined messages and identify weaknesses in your user security awareness training
- Outlook integration using a menu button for users to scan their email for phishing manually
- Threat intelligence for better threat detection of zero-day threats
A Quick Comparison of IRONSCALES and PhishTitan+SpamTitan:
Did You Know?
cyber attacks begin with phishing
to seamlessly install PhishTitan
estimated global cybercrime cost
to stop & spot a phishing attack
Modular Security for Enterprise-Level Flexibility
TitanHQ has a suite of enterprise solutions for managed service providers. SpamTitan and PhishTitan work together to stop malicious email attacks at the gateway and inline levels.
Effective cybersecurity should be built in layers, so a modular solution allows businesses to layer their protection while providing overlapping detection capabilities. For example, a phishing attack could be flagged as spam, blocked, and quarantined even if threat authors can bypass one layer of your email security. Integrating PhishTitan and SpamTitan acts as layers for a strategic cybersecurity plan so that businesses can have a multifaceted approach that protects users and data without potential incompatibility with disparate solutions.
Working with TitanHQ’s suite of security features, you know that solutions work well together and have no compatibility issues. Along with other TitanHQ security solutions, including security awareness training, archiving, and web content filtering, PhishTitan and SpamTitan are two security layers that block most attacks, starting with a simple email message. Whether it’s a malicious attachment or a push for a business email compromise (BEC) payload, PhishTitan and SpamTitan are particularly effective against BEC attacks, which are becoming more common.
SpamTitan and PhishTitan Close Gaps in M365 Security
Several threats target MS M365 users, and attackers can even buy kits built for bypassing two-factor authentication and hacking M365 accounts. With over 345 million people using it, it’s no surprise that a sophisticated phishing campaign could garner several business email accounts. Purchased kits on darknet markets offer criminals of all skill sets the ability to steal business accounts. This exposes targeted victims to ransomware, malware, account takeover, stolen data, and lost intellectual property.
PhishTitan uses the latest in advanced artificial intelligence. It uses integrated cloud email security (ICES) for email security, a newer technology that connects to an email server to scan and detect phishing. Messages in transit or stored in a user’s inbox can be scanned and quarantined. Administrators aren’t required to make changes to MX records, and configurations in the cloud let administrators connect to PhishTitan within 7 minutes. Machine learning identifies zero-days using behavioral patterns, language models, and heuristics.
Another advantage of PhishTitan’s ICES is its ability to learn new behaviors. Machine learning (ML) is responsible for PhishTitan’s ability to identify the latest threats that haven’t been seen in the wild. TitanHQ contributes to the threat intelligence industry, so new behaviors are shared and researched between experts. Results from this research can be incorporated into email security data models.
Because MS M365 is a primary target for threat actors, using PhishTitan adds a layer of security to your email server should native M365 security fail. The added layer improves protection against email-based threats, including messages with malicious attachments or other sophisticated payloads.
SpamTitan is a TitanHQ product that offers an additional layer of protection against spam. Spammers target business email addresses, and M365 spam filtering might miss sophisticated strategies built to bypass Microsoft’s native spam filters. By integrating SpamTitan’s secure email gateway (SEG), administrators block spam from reaching the email server. The benefit of proactively blocking spam messages is that your server resources – CPU and storage resources – don’t need to process nuisance messages.
An email server may handle thousands of messages for large businesses daily. Without spam filtering, the email server environment might store and process thousands of messages, which wastes money. Gigabytes of spam stored on corporate servers could cost millions yearly as the server accumulates more spam messages. For individuals deleting a few spam messages daily, servers don’t need many resources. In an enterprise, a few messages multiplied by a few thousand employees adds up year to year.
SpamTitan’s SEG blocks incoming nuisance messages, and PhishTitan’s ICES scans messages inside M365 for malicious content. Together, the two cybersecurity solutions stop most threats that could lead to ransomware, BEC, malware installation, credential theft, and other data breaches.
PhishTitans' current performance has been sensational – for every 80,000 emails received, PhishTitan is catching 20 unique and sophisticated phishing attacks that Microsoft’s elite and expensive E5 premium security is missing.
Benefits of PhishTitan and SpamTitan Integration
Microsoft M365 has integrated security, but it’s insufficient to stop sophisticated attacks explicitly built to bypass it. PhishTitan and SpamTitan complement your M365 security and provide additional protection using artificial intelligence and threat intelligence gathered by researchers. Capterra visitors rate SpamTitan 4.5 out of 5 stars. PhishTitan is a new complementary service to SpamTitan, and it has the same highly rated customer service, ease of use, and support benefits.
“As a TitanHQ partner, we have used all their other products to help secure our customers. The addition of PhishTitan shows that TitanHQ is ever-evolving and advancing its tool stack to help businesses protect their data. PhishTitan is helping us layer in more protection right inside the M365 mailbox. With threat actors now having the assistance of AI to help them form their malicious email attacks, it is more important now than ever for us to utilize an AI-driven tool like PhishTitan.”
Hunter McFadden, Owner, Greencube.
PhishTitan integrates natural language processing (NLP) to detect common patterns in malicious messages. These messages often include attachments, which can be challenging to identify with an untrained eye. Employees might miss common phishing strategies, but PhishTitan’s NLP identifies them and quarantines messages. Administrators can later review messages and see the number of messages blocked by the PhishTitan and SpamTitan technology.
The artificial intelligence included with PhishTitan and SpamTitan learns changes in the threat landscape to identify zero-day threats better. SpamTitan has an accuracy of 99.9%. PhishTitan is built by the same SpamTitan developers and supported by world-class customer service. Set up can be done within 10 minutes and runs in the cloud. The cloud-based system benefits managed service providers responsible for numerous clients and their email security.
Maximize Value with our Standard Plan
Protect email before, during, and after inbox delivery with MX filtering and ICES protection.
With SpamTitan and PhishTitan working together, you are protected before, during, and after the email's journey to the inbox. It’s the perfect combination to give you total email protection.
You can get started with PhishTitan and SpamTitan by booking a personalized demo today.

Susan Morrow
- PHISHING PROTECTION
TitanHQ vs IRONSCALES Comparison FAQs
Phishing messages typically contain indicators of malicious intent, such as links to spoof landing pages; these links have a Uniform Resource Identifier (URI) that points to the landing page used to steal login credentials and other data. An anti-phishing filter detects malicious URIs by comparing them to a database of known phishing URIs. Advanced anti-phishing filters use AI-enabled measures to detect and filter malicious emails, using multiple techniques to look for signals of phishing.
Email phishing filters help with both Inbound Email Filtering to prevent cyber-attacks and Outbound Email Filtering to ensure an organization maintains a positive reputation by stopping any inadvertent spam or malicious content being sent in a company’s name.
Effective email phishing protection involves using an advanced, AI-enabled email filtering solution, predictive analysis to prevent zero-minute attacks, DNS filtering, and other human-centric measures such as employee phishing training and security awareness training. By applying layers of protection, even evolving threats, such as zero-minute and zero-day attacks, can be prevented.
Traditional anti-phishing filters scan the source code of email content and landing pages to detect known malicious signatures. However, attackers who have evolved tactics to evade traditional phishing detection have circumvented this static detection method. For example, polymorphic malware and content can generate undetectable dynamic signatures that fool conventional anti-phishing filters. This ability to rapidly change malware signatures has led to the development of advanced anti-phishing.
PhishTitan is an example of an advanced email phishing filter. To detect phishing emails, PhishTitan uses several techniques: Real-Time Blacklists (RBLs): identify and block spam from recognized spam-supporting ISPs. Bayesian Analysis: self-learning that improves as it learns. Auto Learning: AI-enable to pre-empt cyberthreats and thought pattern detection in real-time. Heuristics: examines emails for suspicious elements such as malware.
Talk to our Team today

