The high levels of phishing success are due to the insidious nature of the vector; as computing has become ubiquitous, human operators have been trained to react to specific triggers when using a computer. The 'urge to click' is one such trigger that is harnessed for good in helping to simplify interactions between computers and humans. However, these same behaviors are exploited by cybercriminals who manipulate an employee's trust, urge to click, or fears and concerns.
Scammers are masters of social engineering, and they use phishing to execute control of an employee's behavior, which is then used to help hack a company.
This guide to phishing training for employees will take you through the details of how phishing works and why phishing training for employees can help protect your organization from this most harmful cyber threat.
The Revolving Door of Phishing
Phishing emails and other phishing mechanisms are ideal for cybercriminals because they are the touchpoint between the outside world and the corporate network. If a scammer can open that door, they will have free reign to escalate privileges, install ransomware, steal data, and trick staff into paying money into a hacker's bank account. The way to open the door is to get an employee to (inadvertently) welcome the hacker.
How Phishing Exploits People and Behavior?
One of the reasons for the success of phishing as a cybercrime tool is that cybercriminals can modify phishing techniques and social engineering tactics to trick employees and evade detection. A recent example of evasion tactics was the exploitation of the popular email mass mailing tool Constant Contact by the hacking group known as NOBELIUM.
The attackers hacked into the Constant Contact account of the United States Agency for International Development (USAID) and used the account to send legitimate-looking emails to employees in over 150 organizations. The phishing emails were laden with malicious links, but because they were seemingly from a legitimate government agency, the phishing emails fooled recipients.
The campaign by NOBELIUM has continued to evolve, with a subsequent version using an HTML file attachment in a spear-phishing email. Once the recipient opened the file, JavaScript contained in the HTML file executed and began a series of events that resulted in a chain of infection.
Exploiting human behavior is a core element of phishing campaigns. Simulated phishing training replicates this to help employees spot the signs of social engineering.
Exploiting New Technology to Phish and Exploit Employees
This ability to continuously evolute phishing tactics is why scammers use phishing as the preferred tool for initial organizational access.
Evasion techniques follow the technology landscape. For example, the latest technology used by cybercriminals is Malicious AI. ChatGPT, an AI-enabled chatbot model, is an example of a tool that has been developed for legitimate use, but cybercriminals are now exploiting it. According to a recent paper, Creatively malicious prompt engineering, the authors Andrew Patel and Jason Sattler explain how ChatGPT can generate phishing and spear phishing emails.
One of the benefits to cybercriminals offered by ChatGPT is that people with poor language skills or non-English speakers can use the tool to generate sophisticated spear-phishing campaigns.
A recent advisory from Check Point Research (CPR) has found evidence that the cybercriminal community is using ChatGPT, with dark web forums discussing ways to exploit the chatbot.
ENISAlist of Emerging Phishing Threats
More realistic phishing simulations can be created by observing how technology and working environments evolve. The European Union Agency for Cybersecurity (ENISA) watches the trends in the threat landscape. The ENISA Threat Landscape 2022 report states that phishing increases are due to the following:
“Advances in the sophistication of phishing, user fatigue, and targeted, context-based phishing have led to this rise.”
The report also lists some of the core landscape features. Many of these pullout notices could lend themselves to the evolution of phishing tactics as the decade unfolds:
- Consent phishing: Consent phishing encourages users to click to grant the attacker access and permissions to applications and services.
- Data compromise is increasing year on year: The central role of data in our society and its collection is proving a gold mine to hackers.
- Machine Learning (ML) models: ML models are a new target for attacks, and we may see phishing campaigns focus on this area.
- AI-enabled disinformation and deep fakes: Used for misinformation, but the technology lends itself to social engineering attacks and phishing.
More Phishing Tactics and Techniques
The evolution of phishing has allowed cybercriminals to develop a rich source of techniques and tactics. The following is not an exhaustive list, as phishing tactics change with technology and working environments and take advantage of opportunities as they arise. However, the techniques shown below are some of the most common in the phishing landscape and should be noted:
Hijacked Email Systems
The Constant Contact hijack by NOBELIUM shows the efforts that hackers will make to disguise a phishing email. By making the email look as legitimate as possible, including a real-looking email address, the recipient is more likely to believe the email is legit and therefore feel confident about clicking a (malicious) link or downloading an (infected) attachment. This also makes detecting a suspicious email by traditional email gateway solutions less likely. This is why employee phishing training is critical in preventing successful phishing incidents.
Sophisticated Social Engineering
Phishing is often backed by sophisticated social engineering. Fraudsters often use surveillance and intelligence-gathering before embarking on a targeted phishing campaign. The intelligence garnered will help the scammer create believable emails that help build trust with the target employee. Using AI-enabled technologies such as deep fakes and AI-enabled chatbots is likely to make social engineering even more sophisticated and more difficult for employees to detect phishing unless the employee is well-trained.
Evasion Tactics and Email Gateways
Traditional email gateways are no match for evasive phishing emails. In 2021, 2 million phishing emails bypassed older-tech email protection. Name spoofing is used to circumvent technology to allow the phishing email to land in the target employee's inbox. Other evasion tactics include:
- Hiding malicious links inside documents.
- Changing the format of HTML pages to hide common elements from detection engines.
- Using images instead of text to avoid detection.
Evasion tactics are ones to watch as hackers continuously avoid detection to ensure a successful breach.
Brand Hijacking and Spoofing
Trust is a core element of all phishing and associated social engineering attacks. A scammer will use many tactics to build up trust with the recipient. For example, spoofing common brands is a well-known technique to trick employees into thinking they are dealing with a legitimate company. The more famous the brand, the better. Of the 25 most impersonated brands, the top five in 2022 were:
- Microsoft
- Credit Agricole
- La Banque Postale
Other brands making the cut included PayPal and Netflix.
However, it should be noted that when a cybercriminal targets a company and its employees, the scammer will collect information on the company’s suppliers, technology vendors, and other third-parties. This information is used to create phishing campaigns based on the spoofing of specific brands used by the organization. For example, a company may use a collaboration tool such as Slack.The fraudsters will then create a phishing campaign that is designed to steal employee login credentials to Slack.
Consent Phishing
You will have noticed the use of “consent request boxes” when you create a new account with an app or share information online. Consent phishing relies on in-built systems used by protocols such as OAuth 2.0 and the “urge to click”. Fraudsters register legitimate-sounding apps such as "Enable4Calc" to trick OAuth 2.0 providers and users. The apps trick users into consenting to share their data. This is followed by fraudsters beginning the campaign with a phishing message containing a link to the malicious app. If the employee clicks the link, the app opens and generates an OAuth 2.0 consent box. If the employee clicks to consent to share their data, the app generates an authorization code, which is sent to the attacker. This allows the attackers to legitimately access data, including personal data, contacts, and so on.
Smishing
Text-based phishing or smishing has grown alongside the increasing use of mobile devices at work. Smishing works the same way email phishing works, and targeted smishing attacks are common. The only difference is that the malicious link is in a mobile message rather than an email. In 2021, almost three-quarters of companies experienced a smishing attack.
Fake QR Codes and QR Code Phishing
Around 84% of smartphone users have scanned a QR code at least once, and over 34% scan QR codes at least weekly. Unfortunately, cybercriminals innovate around new and popular technologies, so QR codes offer another way to phish employees. “QR code phishing” was highlighted in a 2022 warning from the FBI on QR code phishing. The FBI warned about hackers using QR codes to hack corporate networks by tampering with the QR codes and replacing legitimate codes with malicious codes.
Bypassing Other Technological Measures such as MFA
The use of multiple authentication factors (MFA or 2FA) is not a guarantee of safety from phishing. MFA is in the sights of cybercriminals who have worked out ways to circumvent this additional layer of security: researchers have identified toolkits for sale on the dark web that bypass two-factor authentication. But, again, technology alone cannot thwart cybercriminals. Phishing and other security training for employees are vital to combat cyber threats.
Stats title goes here. goes here
Title Goes Here like thisTitle Goes Here like this
Title Goes Here like this
Title Goes Here like this
Title Goes Here like thisTitle Goes Here like this
Why use Phishing Training with Employees?
As demonstrated, phishing is a complicated and sophisticated attack that is increasingly hard to prevent using technology solutions alone. Therefore, as part of a comprehensive phishing prevention program, employees must be trained to recognize the signs of a wide range of phishing attacks.
This is achieved by using phishing training for employees. Simulated phishing exercises are part of a dedicated training program that builds a culture of security in a company and creates a human firewall that protects the organization from cyber threats. The Aberdeen Group offers an insight into the effectiveness of security awareness training:
“reduction in risk of about 50%; a median annual return on investment of about 5-times; and a reduction in the “long tail” of risk from phishing attacks of more than 2.5 times.”
Phishing simulation solutions provide a platform to generate, deliver, and track simulated phishing messages sent to employees. In addition, the phishing simulations offer intensive training sessions focusing on the many aspects of phishing attacks. SafeTitan is a cloud-based Cyber Security Awareness and Training platform developed to assist in building a human firewall and a security culture that encourages positive security behavior.
Phishing simulation is integral to SafeTitan's Cyber Security Awareness and Training platform. The phishing simulator is controlled centrally, administering and managing simulated phishing campaigns from a central console. In addition, thousands of phishing email templates provide a rich library of ready-to-use and adjustable fake phishing emails.
The campaigns generated using SafeTitan are used to educate employees on how to spot and stop phishing, preventing security breaches, data exposure, and ransomware infection.
Phishing employees using SafeTitan simulated phishing provides tangible benefits
- Easily generates simulated phishing campaigns that reflect real world threats.
- Creates tailored phishing campaigns to train employees at high risk of threats such as Business Email Compromise (BEC), other financial fraud, and ransomware attacks.
- Enables employees to be easily and regularly trained and thus keep ahead of emerging threats.
- Provides contextual feedback to employees as part of the training so that they develop a deeper understanding of the impact of phishing.
- Generates real-time metrics to allow further tailoring of simulated phishing sessions to improve the effectiveness of the training.
- Integrates with other wide-ranging anti-phishing training so that employees have a holistic approach to handling phishing attacks.
Phishing Training with SafeTitan
There are many security awareness training packages on the market. Choosing the best one for your organization can be challenging. However, it is essential to consider the comprehensive nature of any security awareness solution offering.
Security awareness training must focus on changing negative security behavior into positive actions. This comes from a rounded, knowledge-based understanding of security, across the board, from phishing to security behaviors such as poor password hygiene. In addition, security awareness training must address the behavior of employees at an individual level.
SafeTitan security awareness training uses behavior-driven awareness training to change poor security patterns and create a security-first mindset throughout your organization. SafeTitan uses cutting-edge behavioral research as the basis for the SafeTitan solution.
To achieve this all-around approach to empowering employees and building positive security behaviors, SafeTitan provides a comprehensive suite of solutions. It is much more than a phishing simulation platform: SafeTitan is a defense-in-depth training solution designed to prevent human-centric cyber-attacks.
Some of the core features that make SafeTitan stand out from the crowded security awareness training marketplace are:
- Thousands of email templates to make phishing employees more targeted.
- Integrates with a broader security awareness training platform for comprehensive security training.
- Direct email injection support allows MSPs to deliver phishing simulations directly to user inboxes. This saves time and effort, with no need to configure allowed lists and firewalls.
- Ease of onboarding, delivery, and management by an MSP, which is perfect for smaller organizations.
- Exceptional support.
- Engaging, interactive, and effective content.
- Cost-effective ($1.08 per user/per month)
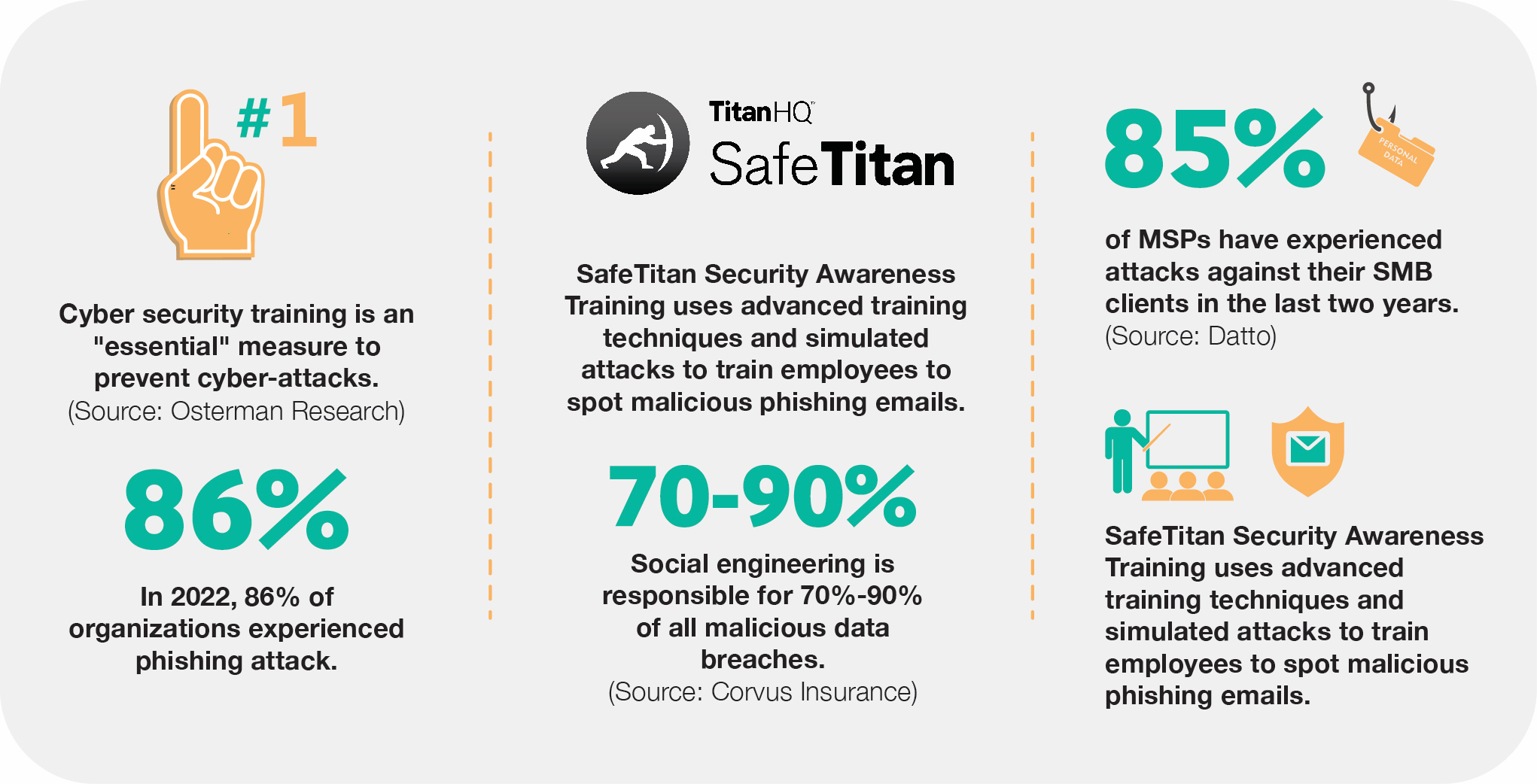
Cybersecurity training is an "essential" measure to prevent cyber-attacks.
Broader Aspects of Phishing Training
SafeTitan excels at building broad, comprehensive training for employees. This is an important differentiator from other competitors in the security awareness arena. Phishing simulations must be delivered as part of a wider, multi-layered, human-centric approach to security. Behavior only changes with repeated training that builds upon learning sessions. As well as providing phishing training for employees, SafeTitan delivers training in other areas, including:
Clean Desk Policy (General awareness)
SafeTitan training educates employees about the importance of a “clean desk.” A “Clean Desk Policy” is a requirement of regulations such as ISO 27001. A clean or tidy desk is also an vital element of general security hygiene, which includes password hygiene, data awareness, and awareness of data exposure via email.
Social Engineering Explored
Check Point Research (CPR) points out that social networks are the most likely to be imitated to steal data, with business social site LinkedIn associated with 52% of all phishing-related attacks globally. Therefore, cyber security awareness and phishing simulations must include training in social engineering tactics such as:
- Social phishing types: How social media is used to steal information.
- Oversharing: Why putting out too much personal or corporate information on a social media site can lead to social engineering and spear phishing.
- Malicious social links: How social media links can be malicious and used as part of a phishing exercise.
- Fake accounts: How to spot fake social accounts that are used to socially engineer employees.
Social engineering is responsible for 70% to 90% of all malicious data breaches.
Staying Safe from Identity Theft
Identity theft is behind many scams and fraud events. In 2021, the FTC received 5.7 million total fraud and identity theft reports, with $2.8 billion lost to imposter scams. The data behind an identity is Personally Identifiable Information (PII). Employees should be educated about what PII is and how to ensure it is not exposed. A cyber security awareness program includes training on safe data protection and destruction and personal data awareness.
Online Security Fundamentals
Safe online browsing is an intrinsic part of anti-phishing measures. The problem is stark, with statistics from Google’s Safe Browsing research showing that over 4.2 million warnings were issued on December 4th, 2022 alone. Employees should be trained in how cybercriminals trick them into navigating to infected and malicious websites.
Mobile Security
Checkpoint research on mobile security found that 46% of organizations had at least one employee download a malicious mobile app. Smishing is also a mobile threat that is increasingly targeting employees. Security awareness training should include mobile security that encourages good security behavior involving mobile devices, that is, safe app downloads, device replacement safe procedures, and safe surfing from a mobile device.
Why Phishing Training is an Investment?
Phishing is costly, with estimates from The Ponemon Institute coming in at around $15.4 million annually for larger organizations. And according to the 2022 Verizon Data Breach Investigations Report (DBIR), even very small companies with less than 10 employees are at risk from Business Email Compromise (BEC), credential theft, and social engineering - all associated with phishing.
Cyber-attacks are costly and include tangible and intangible costs related to IT system downtime, IT support, productivity losses, and brand damage. An Osterman report highlights cyber security training as an "essential" measure to prevent cyber-attacks.
Phishing training for employees builds a human firewall around your organization, making it much harder for cybercriminals to gain unauthorized access to company resources. By using phishing and broader security awareness training, your organization is investing in cyber security threat mitigation.
Phishing training and security awareness are recognized across industry and in standards and regulations as vital to security preparedness. Also, many Cyber Security Insurance policies require that phishing training is performed.
Two Examples of Phishing Training Exercises
Simulated phishing exercises should reflect the real-world threats to your industry sector and employee roles. Below are some examples of phishing training exercises that can be created using SafeTitan:
Business Email Compromise (BEC) Scam
BEC scams often target employees in the finance or accounts payable departments. However, they also focus on C-level executives, including the CEO. Create a simulated phishing training exercise that tests these employees on potential BEC scams.
Note: Use SafeTitan’s email templates to create this phishing exercise.
Cybercriminals carrying out BEC scams do their homework and will have gathered intelligence on your company. Therefore, the email should contain the following elements:
- Create an email that looks like it has come from a known vendor of your company.
- Ensure the email address domain is similar (but not the same) as the vendor's email domain.
- Target specific employees most at risk of BEC fraud.
- Send out the email with an attached invoice saying that the invoice has an "updated mailing address."
- Capture the employee's reaction using metrics: do they attempt to open the invoice? SafeTitan can be configured to intervene when an employee performs a dangerous action and provide contextual learning to help the employee understand why that behaviour will lead to a cyber-attack.
Office 365 Scam
Microsoft is one of the most spoofed brands. Phishers use well-known brands to send mass phishing emails to many employees across multiple departments and organizations.
Note: Use the templates available in SafeTitan to create an Office 365 branded email and a landing page that is designed to collect Office 365 login credentials.
- Create an email that looks like it has come from Microsoft regarding an Office 365 account closure. Write the message written in such as a way as to worry the reader; for example:
"Hello, you have requested to close your Office 365 account. This will take effect in 24 hours unless you cancel the request using the link below. If your account closes, you will have no further access to pay slips, work documents, emails, etc."
- Add a link to the email. This link, if clicked, takes the employee to the branded landing page.
- The landing page will be designed to capture login credentials. If the employee enters these logon credentials, SafeTitan will record this and provide contextual training to the employee to show them why this is a bad idea.
How an MSP can Deliver Phishing Training for Employees?
SMBs (small to medium-sized organizations) are as much at risk of phishing as their larger counterparts. According to the Verizon 2022 DBIR, 61% of SMBs experienced cyber-attacks. However, finding the time, resources, and security skills to deliver consistent and regular employee phishing training can be more challenging for a smaller company. But security training is vital to keep an SMB safe:
Research by TitanHQ has found that regular security awareness training using SafeTitan reduces susceptibility to phishing to under 3%. Notably, this result is even better than the Osterman Report data, which found that only 11% of employees could spot a phishing email before phishing training. In contrast, after training, 64% could detect phishing emails.
This low level of phishing susceptibility will ensure that an organization can significantly improve its security posture; unfortunately, only 32% of small businesses carry out phishing training for employees.
This is where a managed service provider (MSP) comes in. An MSP can offer managed security services to SMBs. MSPs that deliver security services, including phishing training, have specialist personnel and knowledge that allows them to create effective and tailored phishing simulation and security training campaigns.
The MSP is also skilled in interpreting the metrics output from security training solutions such as SafeTitan. Using an MSP to deliver phishing training for employees is an ideal way for SMBs to have exceptional security training for employees that protects their organization from the expensive costs associated with a cyber-attack.
SafeTitan is a solution that has been designed to be delivered both in-house and via an MSP. TitanHQ offer MSPs a unique selling package that provides them with an exceptional training service for clients that delivers regular income.
Research from Datto points out that 85% of MSPs have experienced attacks against their SMB clients in the last two years. Any MSP offering a solution that delivers world-class training in security will give that MSP a compelling competitive edge.
85% of MSPs have experienced attacks against their SMB clients in the last two years.
Comprehensive Security Training from SafeTitan
SafeTitan is a powerful and inventive technology that generates realistic and relevant simulated phishing campaigns to empower your employees against phishing. TitanHQ is the world-renowned security vendor behind SafeTitan, bringing award-winning exceptional customer support to back the use of SafeTitan. G2 and Gartner reviews consistently place TitanHQ products as high-performance. Some of the SafeTitan features that have helped to make it a phenomenal security training platform include:
- Is designed using a highly skilled content creation team in-house with extensive experience.
- Has an easy onboarding process.
- Has a proactive product approach, always staying current and incorporating emerging threats.
- Provides high quality content and an extensive set of functionalities.
- Offers easy integrations with Azure, OKTA, Google, and other Active Directories.
- Guarantees rapid setup.
- Provides ease of user management.
- Ensures that every employee and other stakeholders involved in training are empowered and become part of the human firewall that protects your corporate infrastructure.
What about SafeTitan and an MSP?
Any MSP choosing SafeTitan to deliver security training to their client base will benefit from:
- Easy MSP onboarding. For example, an Azure-based MSP will be up and running and begin to receive the first phishing simulation in less than 10 minutes.
- Easy for MSPs to manage customer(s).
- Mass phishing campaigns, training and Direct Email Injection supported.
- Full reporting capability.
- Mass AUTO Campaigns, which will be available by the end of Q1 2023.
Conclusion
Phishing is one of the leading causes of costly data breaches. IBM's 2022 Cost of Data Breach Report found that the average cost of data breaches rose from $4.24m in 2021 to $4.35m in 2022.
Therefore, security awareness and phishing training for employees must become a recognized and vital part of a security strategy. As phishing and cyber-security tactics evolve to evade detection by traditional security tools, organizations can no longer rely on technology to combat the onslaught of evolving phishing threats.
Instead, an organization must turn to its people and make security everyone’s business to create a human firewall. As cybercriminals continue to challenge companies of all sizes, having a tool that empowers employees is a decisive way to stop scammers that exploit human behavior.
What Employees Can Do To Be Safe From Phishing?
Prevention is always better than cure. Now that your team knows what to look out for in phishing emails, they can also take the following protective measures to ensure they secure the integrity of the organization’s data. Employees should:
- Remember that emails from legitimate businesses will never ask for your personal information, including usernames and passwords.
- Not click on any links in an unsolicited email or text. Better still, refrain from opening such emails or text messages. Alternatively, look up the said company’s contact information online and call them to verify the legitimacy of any request.
- Carefully examine the email address by hovering over it, the URL, the spellings in the body text, and the logo or brand image if any. On careful observation, you will be able to notice slight differences that might not otherwise be obvious.
- Be aware of what you download and wary of opening attachments you receive from unknown sources.
- Remember to set up multi-factor authentication wherever possible and do not ever disable it.
- Be careful about the information shared online, especially on social media platforms. People tend to share a lot of personal information on social media, from kids’ names and pet’s names, to birthdays and everything else. They don’t realize that they’re giving scammers all the information they need to figure out passwords or answer your security questions.
What To Do If You’ve Been Phished?
If an employee has fallen prey to a phishing attack, here are a few things you can get them to do immediately:
-
Ask them to note down as many details they can recall while the incident is still fresh in their mind. Useful details could be usernames, passwords, or account information they may have inadvertently given out.
- Change passwords on the affected accounts immediately and any other application where they may have used the same password. New passwords should be unique and strong.
- Ensure multi-factor authentication is turned on for every account where possible.
- If credit card or bank account information has been shared, ensure that the respective service providers are informed too.
- Phishing attacks leading to loss of money or identity theft need to be reported to local law enforcement.
What Does A Phishing Campaign Test Email Contain?
Cybercriminals are adept at developing phishing campaigns that target employees. Therefore, organizations should also establish dedicated phishing campaigns to counteract these malicious attacks. Additionally, a phishing campaign should take certain phishing factors into account; for example, will your test phishing email include:
Malicious links: will the test email contain malicious links? This will test an employee’s ability to spot dangerous links. The phishing simulator will capture if an employee clicks on a malicious link in the test email.
Malicious attachment: malicious attachments contain files used to infect devices with malware or embedded links that take recipients to a malicious website. The phishing test will note if an employee downloads or opens a malicious attachment.
Malicious website:
Many phishing emails contain links to malicious websites where cybercriminals attempt to collect data or credentials. For example, a phishing campaign may want to test an employee’s reaction to landing on a malicious website that looks like a legitimate site they use regularly. The phishing simulator will capture if an employee adds data to the web form.
How To Create An Effective Phishing Campaign?
Phishing campaigns should be both tactical and strategic:
Strategic: plan out what you want to achieve from your phishing campaigns. For example, will the phishing campaign be a company-wide exercise that handles general phishing? Or will you augment this campaign with roles-based targeted phishing? Whatever your strategic vision for your phishing campaign, you should reflect the current threat landscape to make the phishing campaign more realistic.
Tactical: once you have your strategic vision, you must work out the tactical steps in making the phishing campaign successful. The tactics will include considerations such as:
- Will the campaign use mock phishing templates available in a phishing simulation platform?
- If using templates, do you need to modify the templates, and who will be responsible for crafting the mock phishing content? How will the test emails reflect a real-world phishing scenario?
- How to tailor fake phishing emails to target specific roles in your organization, for example, test an employee’s response to a BEC attack.
Once a phishing campaign is developed and ready to go, you can begin delivery of the phishing test and record the results. These results, or metrics, will provide insights that can be used to tailor future phishing campaigns further. Effective phishing campaigns must also consider compliance and ensure that stakeholder buy-in is gathered and that the use of personal data in test emails is avoided.
To design and deploy an effective phishing campaign for employees, use a phishing campaign tool intended to deliver behavior-led training.
Employee Phishing Training Questions
Security awareness training includes modules to ensure employees are aware of the risks of phishing. Your employees' education must focus on certain core tricks and ruses used by cybercriminals who carry out phishing attacks. Phishing is all about the manipulation of human behavior:
- Encouraging a click on a malicious URL.
- Entering data into a spoof website.
- Downloading an attachment that contains malware.
As part of security awareness training, employee phishing training questions are provided as interactive quizzes. These questionnaires help educate staff on phishing and related areas, such as password hygiene. Some employee phishing training questions are simple yes-no questions, while others are multiple-choice.
Examples of employee phishing training questions:
"You receive an email from your boss asking for the bank account details of your main client. The email seems urgent, even showing concern over losing the client. Should you?
A. Instantly reply, this seems very important.
B. Call your boss to double-check; this may be a scam."
Other questions may contain images of an actual email; the staff member is then asked to decide if it's genuine or a phishing email. Once the employee chooses, they will be shown further information about the email based on their answer.
Further, questions may be configured to provide a learning opportunity on phishing-related issues, such as: "Is it OK to use the same password for multiple accounts?" The question will contain information about the danger of using the same password.
Phishing Awareness Training
Various agencies and analysts recognize that phishing is the most common method used to initiate a cyber-attack. Around 300,00 phishing attacks happen every three months, and employees are at the front line of phishing attacks; most attacks are targeted and used to gather intelligence or to steal login credentials. With this in mind, it is essential to educate employees of an organization about the dangers of phishing. Phishing awareness training is a dedicated element of security awareness training focusing on phishing. Phishing awareness training is a regular, campaign-based attempt to empower employees with the knowledge to recognize phishing attempts. These phishing attempts may otherwise result in compromised login credentials, malware installation, data theft, and financial losses. Being able to spot the tell-tale signs of phishing means that the employee is much less likely to turn a phishing attempt into a security incident.
Phishing awareness training includes practical sessions involving interactive training and phishing simulation exercises. Some advanced solutions, such as SafeTitan, offer "randomized lures" during a simulated phishing campaign that provide a pseudo-phishing experience, making the phishing awareness training more effective. Employees are given in-line training if they click a spoof malicious link or download an attachment in one of the fake phishing emails.
Phishing Email Training
Email phishing comes in many forms, including mass mailout, spear-phishing, Clone phishing, and Barrel phishing. Phishing email training is an effective way to educate employees on identifying the various types of phishing emails. Phishing email training is based on the current trends in email phishing, such as targeted attacks that use social engineering to trick employees. Training involves teaching employees' various tactics and tricks to manipulate their behavior. The methods used to deliver this training include different computer-based, interactive, and simulation-led training. Computer-based email training involves providing a variety of interactive quizzes, videos, and other content to employees. Effective phishing email training content is fun and gamified to encourage learning. The content will provide feedback to employees if they show risky behavior and educate employees on how to next deal with a phishing email attempt. Phishing email training also includes the use of phishing simulation exercises. These spoof phishing campaigns can be tailored to suit the threat landscape and an employee's role. Phishing simulators also provide metrics based on the outcome of a phishing simulation exercise. These metrics will allow administrators of a phishing simulation campaign to adjust tactics to improve learning. Phishing email training should always be behavior-driven, as it is human behavior that cybercriminals manipulate during an email phishing attack.
Anti-Phishing Training
Phishing is overwhelming for companies to deal with unless they implement Anti-phishing training. With almost all companies experiencing a phishing attack, anti-phishing training is not a nice to have but a must-have. Employees are at the front line of these attacks, with many attackers generating target phishing emails based on intelligence gathered on a company and staff. AI tools such as ChatGPT are helping in this endeavor, allowing cybercriminals to create believable emails that are hard to detect. However, employees can be trained to identify these sophisticated email and other channel phishing attempts. When used regularly, anti-phishing training will improve an employee's ability to identify a phishing attempt and teach them how best to respond. The training involves teaching employees across the organization, including at the C-level, about the crime of phishing. The training will detail phishing, the tactics used to manipulate behavior, and associated problems such as safe internet use and password hygiene. All of these anti-phishing training elements will work towards creating a highly educated workforce. Regular, engaging, and behavior-focused anti-phishing training develops a security mindset and a culture of security. When phishing simulation exercises are used alongside regular phishing training, the results are exceptional: SafeTitan's phishing simulation platform has decreased employee susceptibility to phishing by 92%.
Email Phishing Training
Phishing comes in many forms, with cybercriminals exploiting whatever channel is most effective. Phishing can come through phone calls, social media posts, and mobile messages. However, email phishing is the most well-known and used form of phishing. Email phishing has many variants, including Phishing, Spear phishing, Whaling, Clone phishing, and Barrel phishing. Each of these forms of phishing represents a different technique. For example, spear phishing is typically used to target a specific employee in an organization. Whaling is also a form of spear phishing but targets C-level executives such as a CEO. These many email phishing variants represent different end goals, such as credential theft, Business Email Compromise, and ransomware infection. To ensure that phishing training is practical, email phishing training will deliver tailored education to employees to address the risks associated with phishing variants. Email phishing training uses simulated phishing platforms to send employees tailored spoof phishing emails. Upon receiving these fake phishing emails, the employee will have in-line training based on their response. Metrics based on these responses will allow administrators of the phishing simulation platform to configure increasingly effective test campaigns. Over time and with regular training, employees will learn to identify risky emails.
Phishing Security Awareness Training
Security awareness training provides your staff with the knowledge and methods to protect your organization and themselves against cyber-attacks and accidental data exposure. The latest research shows that 82% of data breaches involve a human element, so focusing on risky behaviors is an excellent way to prevent cyber-attacks. Many of these cyber-attacks begin with phishing. Phishing awareness is a central part of security awareness training. Phishing security awareness training imbues individuals with the knowledge needed to spot phishing emails and phishing via other channels, such as mobile messages. Phishing security awareness training is vital to any organization's cybersecurity strategy. A positive outcome of an effective phishing security awareness training program is creating a culture of security where the identification and response to phishing becomes intrinsic and positive employee behavior that prevents cyber-attacks. This concerted effort to stop threats before becoming cyber incidents helps further forge a security culture. Once a security culture is established, security becomes a natural response, strengthened by a highly knowledgeable workforce. Establishing this security culture requires a highly effective security awareness training program that strongly focuses on phishing.
Cyber Security Phishing Awareness Training
Cybercriminals are adept at exploiting human behavior by utilizing digital tools, such as email. Cyber security phishing awareness training educates employees about how cybercriminals use these tools to manipulate them into performing actions that benefit the attacker. Cyber security phishing awareness training sessions typically include various content that educates employees on the dangers of phishing and how to identify phishing attacks. The range comprises computer-based training materials such as quizzes, videos, and phishing simulation exercises. Other training sessions can include games and interactive sessions that develop and hone employee phishing identification skills. Phishing simulation platforms, like SafeTitan, allow administrators of cyber security phishing awareness training to create fake phishing emails. A simulated phishing campaign is generated from templates and sent to employees across the organization. During the training, in-line teaching is used with employees demonstrating risky behavior; the employee is shown what would have happened if this was an actual phishing email. Spoof phishing emails can be tailored to reflect the risk of specific organizational roles. Also, a centralized dashboard provides metrics showing cyber security awareness campaign progress. These metrics can establish a risk profile for your organization that can be shared with senior management. The metrics also provide insights into employee performance and historical trends to allow adjustment of security awareness campaigns for continuous improvements.
Phishing Email Awareness Training
Phishing is a sophisticated and complex, often multi-part scheme to manipulate users. Phishing results are legendary, including data theft, credential compromise, ransomware infection, and Business Email Compromise (BEC). Because of the insidious nature of phishing scams, one of the most effective ways to stop phishing is to train people to spot phishing emails and SMS messages (SMShing). Phishing email awareness training is a systematic way to deliver this training. Phishing email awareness training comprises a mix of computer-based training sessions, gamified training, interactive videos, and phishing simulations. Training sessions are performed regularly. Advanced phishing email awareness training platforms support training automation and are cloud-based services, making it easy to roll out and manage. Email phishing comes in many forms, including spear phishing, Whaling, Clone phishing, and Barrel phishing. Phishing email awareness training provides education to employees on all types of phishing. Phishing focuses on manipulating human behavior, often adding social engineering. To counteract behavior manipulation, phishing email awareness training must be behavior-led and adaptable to reflect the behaviors of individuals. By having this level of control that reflects how people respond to phishing email awareness training, SafeTitan reduces susceptibility to phishing by 92%.
Phishing Awareness Training for Employees
Phishing awareness training educates staff in detecting phishing and what to do if they inadvertently activate a phishing attack. Phishing training is essential as human-centered attacks that manipulate behavior are the most common way to initiate a cyber-attack. Because cyber-attackers use sophisticated tricks and social engineering, employees find identifying an email phishing attempt challenging unless they are trained to identify these ruses. This training must also be performed regularly as cybercriminals adjust phishing tactics over time. Phishing email awareness training covers a broad spectrum of phishing threats; an effective phishing email awareness training program must reflect all possible threats. However, it is also important to tailor training to ensure that the training material represents specific employee roles and risks. For example, accounts payable employees may be targets of Business Email Compromise (BEC) scams that use phishing. In this case, those employees should be trained in how BEC scams work. Phishing awareness training for employees covers a broad range of topics, including phishing tactics such as the use of malicious links to steal login credentials and how cybercriminals manipulate behaviors such as urgency and fear of missing out (FOMO); password hygiene and security; social engineering trick used to develop trust that can then be abused; and safe internet use.

Susan Morrow
- DATA PROTECTION
- EMAIL PHISING
- EMAIL SECURITY
Talk to our Team today

Phishing Training for Employees FAQs
Phishing is the most common technique employed to hack corporate devices and networks; in 2022, the FBI IC3 received 300,497 reports of phishing with BEC, fraud costing US victims over $2.7 billion. Due to the ubiquitous nature of phishing, phishing training prevents the successful targeting of employees using malicious emails. Phishing training uses mock phishing tests, interactive content, quizzes, and behavior-led sessions to ensure employees can identify and prevent phishing attacks.
According to research, 90% of data breaches use phishing emails as part of the cyber-attack. Training is based on education, informed by analyzing and understanding human behavior. A behavior-led phishing education focuses on changing risky actions that lead to successful cyber-attacks. Phishing education focuses on several areas:
Employees are educated about the many types of phishing. Employees learn how fraudsters use any communication channel to trick and exploit them. Employers should inform employees about all forms of email phishing, including spear phishing, clone phishing, barrel phishing, etc. Other forms of phishing, such as Vishing (phone calls), SMShing (text messages), Whaling, etc., are also part of phishing education for employees.
Phishing training educates employees on the basics of phishing, what a phishing attack looks like, who is at risk, and how to spot tell-tale signs. It includes teaching employees about the dangers of social engineering. Training on phishing types show how cybercriminals will try to build relationships with targeted employees to ensure success. Phishing education for employees educates staff about how an instinct to do a good job, click links, and be helpful, is exploited during a phishing attack
Emails are predominantly the primary type of phishing used to target employees. As such, a focus on email phishing training for employees is essential. As well as using interactive content, email phishing training should include the following:
SafeTitan provides a cloud-based platform to set up, deliver, monitor, and analyze simulated phishing exercises. Fake phishing emails are sent to employees to check their level of education in phishing tactics and tricks. The simulated phishing platform will also deliver contextual learning; when an employee performs a risky behavior associated with the fake phishing email, the platform will pop up a learning exercise to teach them what would happen if this was an actual phishing email.
Regular simulated phishing exercises and regular cyber security awareness training in phishing are essential for achieving excellent education outcomes. In addition, repeated sessions that build on previous education and training will help to make training more effective. Coupling this approach with tailored and roles-based training sessions, and email phishing training for employees, delivers successful training that prevents cyber-attacks.
Cybercriminals are adept at developing phishing campaigns that target employees. Therefore, organizations should also establish dedicated phishing campaigns to counteract these malicious attacks. Additionally, a phishing campaign should take certain phishing factors into account; for example, will your test phishing email include: malicious links, malicious attachments, malicious websites.
Phishing campaigns should be both tactical and strategic: Strategic - plan out what you want to achieve from your phishing campaigns. E.g. will the phishing campaign be a company-wide exercise that handles general phishing? Or roles-based targeted phishing? Tactical: the tactics will include considerations such as: Will the campaign use mock phishing templates available in a phishing simulation platform?
A single click on an infected attachment or input of data into a malicious website can end in severe harm to an organization. Employees will become adept at spotting phishing messages through regular, tailored, behavior-led training. However, phishing evolves, so phishing awareness must be an ongoing commitment that reflects real-world phishing attacks. Repeated phishing awareness training will benefit both the company and the employee by empowering the employee with education.
